NHS progress on cyber security ‘alarming’ following hack attack, say MPs
An influential group of MPs have called the Government’s progress on NHS cyber safety ‘alarming’ following last year’s malware attack.
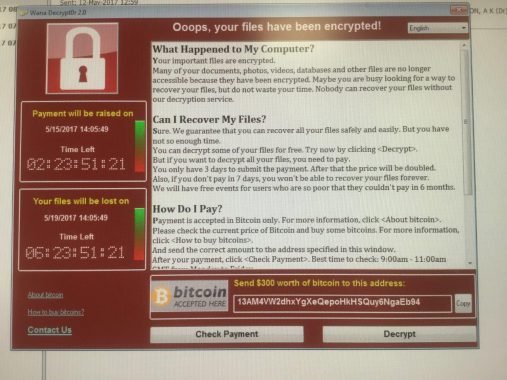
The hacking attack left 595 GP practices locked out of their systems on 12 May 2017, when infected by the malicious ‘WannaCry’ programme which demanded a ransom before it could be unlocked.
The Department of Health and Social Care published a list of 22 ‘lessons learned‘ from the hacking attack in January, which the Public Accounts Committee (PAC) has now given it just over two months to make progress on.
Also by June, the PAC wants to see agreement between national and local NHS leaders on how to target the £21m investment into boosting securty that has been set aside by DHSC.
Its report said: ‘The department and its national bodies should urgently consider and agree implementation plans arising from the recommendations within their Lessons Learned document, prioritising and costing actions, setting a clear timetable, and ensuring national and local roles, responsibilities and oversight arrangements are clear.
‘They should provide an update on progress to the committee by the end of June 2018.’
The committee also wants to see a ‘national estimate of the cost to the NHS’ of last year’s attack, which caused ‘widespread disruption to health services’.
‘More than a third of NHS trusts affected’ and 20,000 hospital appointments and operations were cancelled. Patients were also ‘diverted from five accident and emergency departments that were unable to treat them’, the PAC said.
The report said: ‘Yet the NHS was lucky. If the attack had not happened on a Friday afternoon in the summer and the kill switch to stop the virus spreading had not been found relatively quickly, then the disruption could have been much worse.’
PAC chair Meg Hillier MP said the attack ‘laid bare serious vulnerabilities in the cyber security’ of the NHS.
She said: ‘It is therefore alarming that, nearly a year on from WannaCry, plans to implement the lessons learned are still to be agreed.’
She added: ‘Government must get a grip on the vulnerabilities of and challenges facing local organisations, as well as the financial implications of WannaCry and future attacks across the NHS.
‘Cyber security investment cannot be properly targeted unless this information is collected and understood.’













